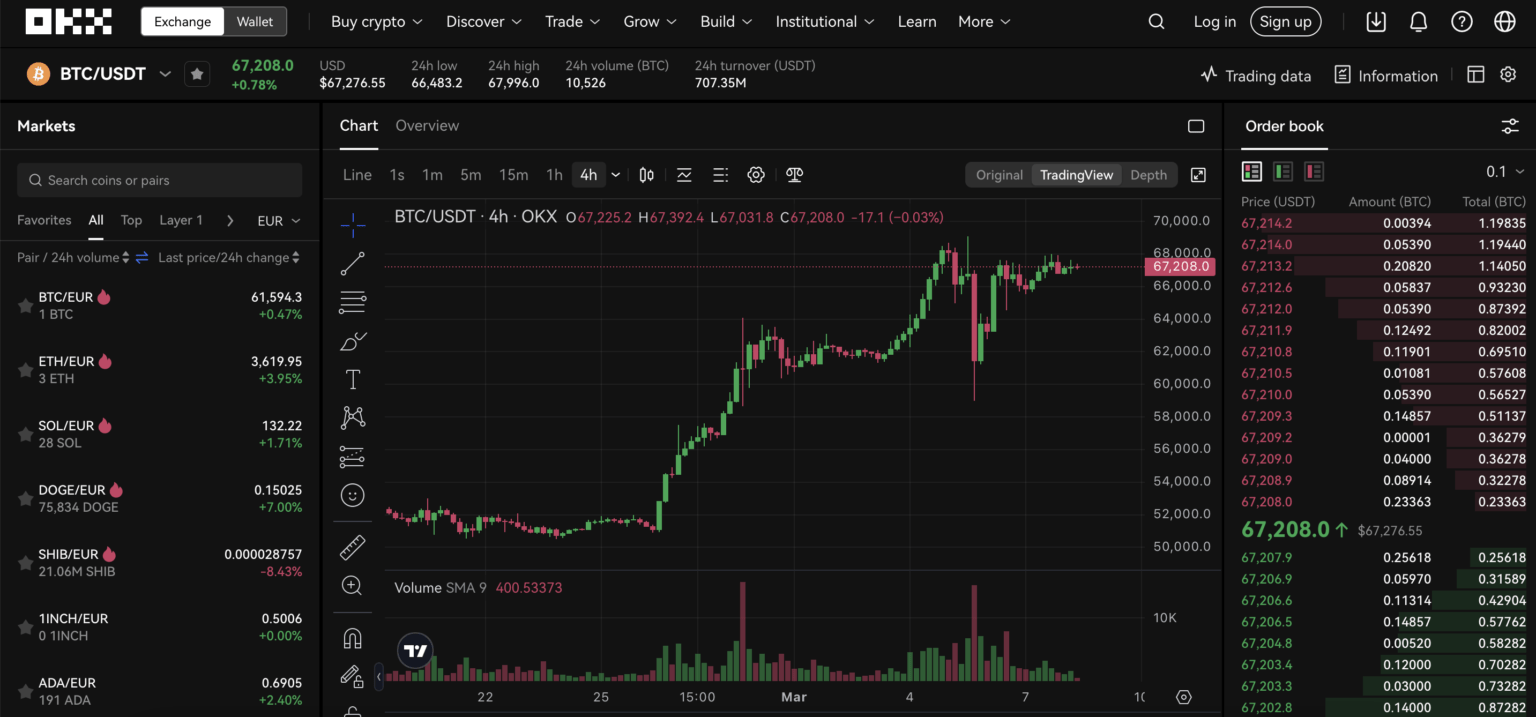
Imagine it’s Tuesday morning, your phone buzzes with a price swing in Ether, and you need to get onto your exchange account fast. You open the OKX app, enter your credentials, and—pause: is this session secure? Did you just type your password on public Wi‑Fi? For active crypto traders in the U.S., the moment of login is not a perfunctory step; it is a junction where usability, security design, and regulatory constraints intersect. This article walks through how OKX’s sign‑in and trading surface work in practice, unpacks common myths about custody and safety, and gives concrete heuristics you can use to choose authentication methods, manage account settings, and reduce the odds of a costly mistake.
I’ll center the discussion on mechanisms—what happens under the hood when you authenticate, trade, or switch between OKX’s centralized exchange and its Web3 wallet—then compare trade‑offs (speed vs. control, convenience vs. recoverability), highlight where the system breaks, and end with simple, decision‑useful rules for U.S. traders. Along the way I’ll point out a few immediate signals to watch, like routine pair delistings that affect liquidity and trading choices.
How OKX Login Actually Works: Mechanisms and Threat Surfaces
At a mechanical level, OKX implements a layered authentication system. Your username and password are the first factor. Mandatory Two‑Factor Authentication (2FA) is the second: OKX supports SMS, time‑based one‑time passwords (TOTP) like Google Authenticator, and biometric methods on mobile devices. The platform also runs AI‑driven threat detection to flag unusual login attempts and military‑grade encryption for stored credentials. For traders, two crucial implications follow.
First, risk is multi‑vector. Centralized protections are strong: OKX keeps over 95% of assets in cold storage with multi‑signature controls and publishes Proof of Reserves (PoR) so users can verify on‑chain backing. Those measures reduce systemic exchange risk (the exchange being insolvent or hacked). But login and session risks are external: phishing sites, browser extension malware, SIM‑swap attacks, and social engineering remain the primary attack routes. The technical boundary here is clear—exchange custody mitigates custodial theft, not credential compromise.
Second, the distinction between centralized account and self‑custodial wallet matters. OKX offers a non‑custodial Web3 wallet where users control private keys and seed phrases. Logins there are fundamentally different: losing a seed phrase means permanent loss, while credential compromise on the centralized side triggers exchange remediation processes. That trade‑off—control versus recoverability—is the conceptual hinge every trader must understand.
Practical Trade-Offs: Speed, Safety, and Compliance for U.S. Users
Traders evaluate platforms along three practical axes: speed (how quickly you can authenticate and execute), safety (probability of losing funds due to fraud or compromise), and compliance (how KYC and regulatory friction affect access). OKX attempts to optimize across all three, but trade‑offs persist.
Speed: Biometric login on mobile is the fastest route to a live session. It lowers friction for time‑sensitive trades (important for spot, margin, or futures strategies) and reduces password re‑entry errors. However, biometric methods are device‑tied: if your phone is lost or wiped, account recovery requires 2FA and KYC steps that can add hours or days—friction that matters if markets move fast.
Safety: TOTP (authenticator apps) is the stronger 2FA choice compared with SMS because SMS is vulnerable to SIM‑swap attacks that have targeted U.S. users aggressively. Combining TOTP with hardware security (when supported) gives the best protection. OKX supports hardware wallet integrations in its Web3 wallet—useful if you move funds off the exchange for custody. But remember: hardware keys protect private keys, not account passwords—both layers need good hygiene.
Compliance: OKX requires KYC and facial liveness checks. For U.S. residents, that means identity verification is non‑optional to trade and withdraw. KYC increases recoverability (it helps you regain access after a lost password) but also adds privacy exposure and potential delays when verification systems flag anomalies. In practice, be ready to submit government ID and follow the liveness prompts during account setup—don’t expect instant anonymous access.
Common Myths vs. Reality
Myth: “If an exchange has cold storage, you cannot lose funds.” Reality: Cold storage and PoR significantly lower counterparty risk but do not eliminate end‑user risk. Phishing, credential theft, and mistakes moving assets to DeFi protocols (smart contract risk) are independent threats. The correct mental model is layered defenses: exchange protections reduce one class of failure; user practices must mitigate the rest.
Myth: “Self‑custody is always safer.” Reality: Self‑custody gives technical control and eliminates counterparty risk, but it places the recovery burden on you. Losing a seed phrase is usually permanent. For a trader, a hybrid model can be optimal: keep trading capital on the exchange for liquidity and speed, while storing long‑term holdings in hardware‑backed self‑custody. The boundary condition is your tolerance for operational complexity and loss of immediate liquidity.
Login-to-Trade Flow: A Decision Framework for U.S. Traders
Here is a practical, repeatable framework—three questions to run through before you log in:
1) What is the trade horizon? If you need sub‑second action (scalping or reacting to news), enable biometric with device unlocking and keep TOTP active as a backup. If trades are infrequent, prefer TOTP plus periodic hardware checks to reduce remote compromise risk.
2) What assets and product types are involved? For spot trades in high‑liquidity assets you can rely on exchange custody and PoR. For complex derivatives (125x leverage is available on some futures), understand that rapid deleveraging or margin calls can cause forced liquidations if your session is interrupted—consider lower leverage if you anticipate connectivity or authentication friction.
3) Will you need quick withdrawals? If you plan to move assets into DeFi or a personal wallet, pre‑link a hardware wallet and practice the withdrawal flow during low volatility. Withdrawals often require recent 2FA and can be subject to exchange withdrawal whitelists or delays triggered by suspicious activity flags.
For a hands‑on how‑to, OKX’s web and mobile login UI includes clear affordances for 2FA setup, device management, and session history. If you want a direct walkthrough resource, see this OKX login guide: okx.
Where the System Breaks: Known Limitations and Failure Modes
There are several realistic failure modes to plan for:
– Credential theft via phishing: attackers create convincing replicas of login pages. Always check domain, use bookmarks, and prefer authenticator apps over SMS.
– SIM‑swap and account takeover: particularly relevant to U.S. telecom environments with socially engineered porting — avoid relying on SMS 2FA alone.
– KYC friction: unusual addresses, VPNs, or rapid device changes can trigger additional verification and temporary freezes that cost time during market moves.
– Delisting impacts: OKX periodically delists spot pairs (for example, newly announced delistings this week remove certain niche tokens). Delistings lower liquidity for affected assets and can turn a marketable order into a messy exit. If you hold small‑cap tokens, be ready to migrate them to a self‑custodial wallet or risk being forced to sell at poor prices before the delisting deadline.
Decision‑Useful Heuristics
– If you trade derivatives or use leverage, prioritize low‑latency authentication (biometrics on a secure device) and keep margin buffers to withstand brief login interruptions.
– If you hold long‑term positions or illiquid tokens, move them to a hardware‑backed self‑custodial wallet and verify recovery seeds offline. Use OKX’s Web3 wallet when you need DApp access, but treat that wallet like a separate custody domain.
– Use TOTP as your baseline 2FA; add hardware keys where available. Disable SMS 2FA unless it’s your only option—then harden your carrier account with a PIN and alerts.
What to Watch Next (Signals and Short‑Term Implications)
– Regulatory signals: U.S. KYC requirements are stable now, but evolving policy or enforcement could change onboarding friction. Watch for changes in withdrawal limits tied to verification tiers.
– Liquidity pruning: routine delistings of niche spot pairs are a recurring signal that exchanges continuously refine listings to improve market quality. For traders holding small‑cap tokens, delisting schedules (and migration windows) should be part of position management.
– Cross‑platform convergence: OKX’s combination of CEX, DEX aggregator, and Web3 wallet creates useful operational flexibility. If cross‑chain bridges and DEX routing improve, traders may shift between centralized order books and permissionless liquidity more often. That flexibility increases optionality but also multiplies security surfaces.
FAQ
Q: Which 2FA method should I use for the best balance of security and convenience?
A: Use a TOTP authenticator app (Google Authenticator or similar) as the baseline because it resists SIM‑swap attacks. For convenience during active trading, enable biometrics on your mobile device; pair that with TOTP as a recovery method. If you require the highest security for large balances, add a hardware security key or move long‑term funds to a hardware wallet.
Q: If I lose access to my phone, how quickly can I get back into my OKX account?
A: Recovery speed depends on what recovery options you prepared in advance. If you saved backup codes and have completed KYC, you can regain access faster—often within hours after verifying identity. Without backups, you will rely on OKX’s support and KYC re‑verification, which can take longer. The practical lesson: record backup codes and keep them in secure, offline storage.
Q: Should I keep trading capital on OKX or transfer everything to a personal wallet?
A: There’s no single right answer. Keep active trading capital on the exchange for speed and liquidity; move long‑term holdings and large sums to hardware‑backed self‑custody. This hybrid approach uses the exchange for execution and custody proofs, and personal wallets for long‑term control.
Q: How do delistings affect my login or trading workflow?
A: Delistings do not typically affect login mechanics, but they do change your liquidity decisions. If a token you hold is announced for delisting, you will need to act within the delisting window—either withdraw the token to a personal wallet or sell it before the pair is removed. Keeping an eye on listing notices and acting early reduces execution risk.
Final takeaway: logging into OKX is a small operation with outsized consequences. Treat authentication as an integrated operational choice—paired with KYC planning, 2FA selection, and a clear custody strategy—and you reduce the chance that a simple login ends in a disproportionate loss. The platform provides robust structural protections like cold storage and PoR, but those protections are complements to—never substitutes for—sound user practice.